Data Protection for Banking & Financial Services

Data Breaches in Banking and Financial Services
In 2017, the Equifax data breach costed the company $425 million. Statistically, financial services institutions are 300 times more likely to be attacked than any other sector, underscoring the need for financial services and banking organizations to safeguard their data. The criticality of the data stored by banks – in the form of social security numbers, credit details, and other personally identifiable information, could cause chaos should it fall in the wrong hands.
The banking industry is no stranger to the ill-effects of losing data. Regulatory non-compliance, loss of credibility and the resultant monetary impact are all driving factors behind their need for safe data backup strategies. We list here a few important considerations for data protection and around the importance of privacy of such protected data.
Financial services institutions are 300 times more likely to be attacked than any other sector, underscoring the need for data protection in financial service industry
Do you have specific requirements or enterprise needs?
Consideration 1: Regulation
One consideration is regulation. Banks are among the most highly regulated industries the world over. Apart from regulations specific to the banking vertical, general geography-specific regulations like SOX and GDPR also apply, not to mention compliances such as PCI-DSS. The need to protect data, retain it for prescribed periods, and prove compliance is probably the highest in this industry vertical. And the penalties for non-compliance just as stiff.
Newer regulations are holding banks more and more accountable for data breaches / losses, and that trend is unlikely to change in the short term. GDPR, the newest in the line of regulations came into effect last year and comes down hard on organizations by fining them as much €20 million (about £17.5 million) or 4% of their global annual revenues, whichever is greater!
Consideration 2: Insider Threats
The first instinct of most security teams is to safeguard against external threats. An often overlooked factor is that one of the major risks to crucial data comes from the inside. Insider threats may not necessarily always be malicious. Employees are human and can make errors – but the fact that they are trusted actors and are on the inside, makes their actions highly significant and vulnerable vectors for data loss.
Employees have direct and indirect access to assets that drive cash flows, competitive advantages (disadvantages) and shareholder value. An accidental (or malicious) actions could put important data at risk. A Forrester research report says that the greatest volume of security breaches (36%) come from employees inadvertently misusing data. That statistic is food for thought while designing your data security plan.
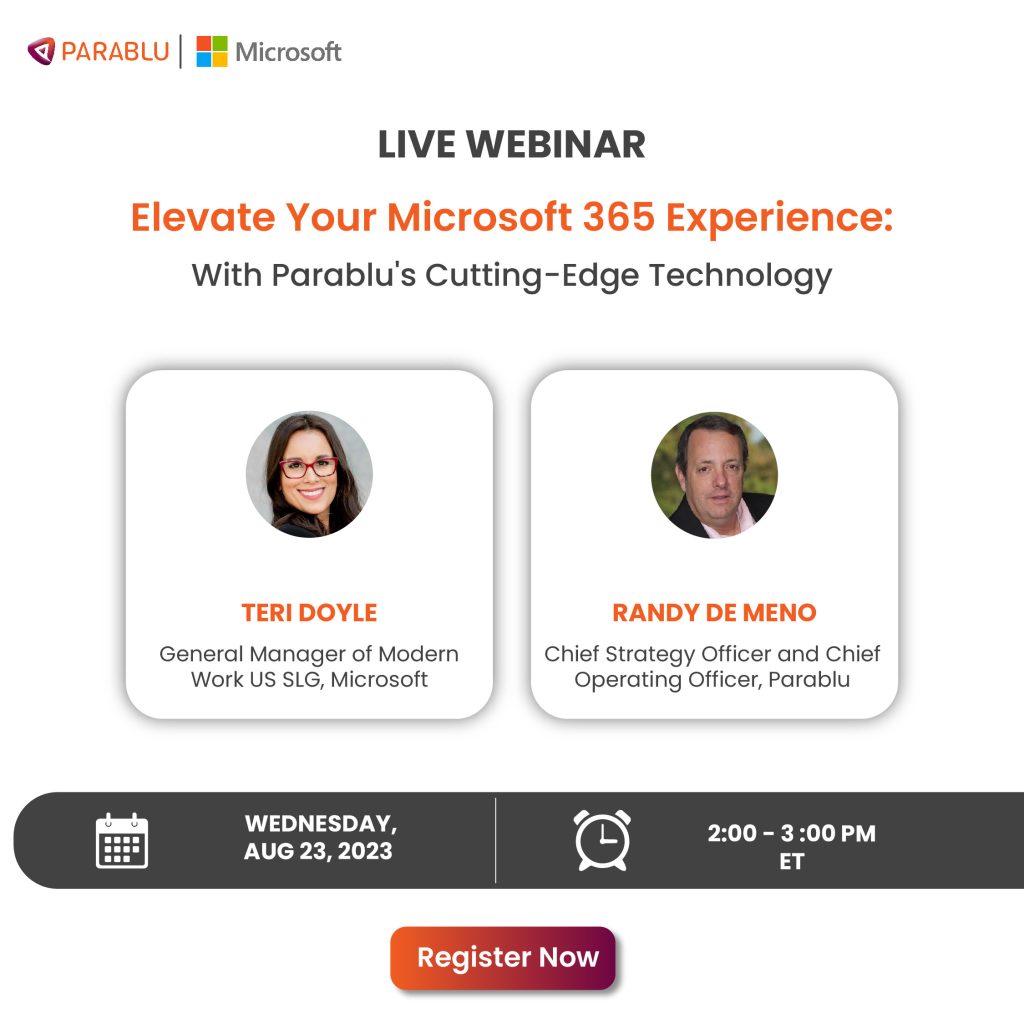
Elevate Your Microsoft 365 Experience: With Parablu’s Cutting-Edge Technology
Discover how you can enhance your M365 user and admin experience. Learn how Parablu’s innovative solutions play a key role..
Watch the webinar
Consideration 3: Malware attacks
Another factor gaining currency is malware attacks. A malware attack has the potential to cripple an entire organization, not to mention the loss of credibility it brings along with it (Equifax is still topping news headlines for the data breach, two years on. Never forget the unforgiving nature of bad PR!). ransomware authors are constantly active with new variants and have proved that they can get around the best security defenses.
Losses due to ransomware go well beyond the ransom that may be paid to the malware author. Negative side effects include bad PR, lost credibility with customers, opportunity costs, etc., which usually tend to overshadow the actual ransom paid. Conventional wisdom now advises that the best defense against ransomware is to have a secure copy of your data which you can go back and retrieve – without being held hostage by the attacker.
The communicable nature of ransomware attacks however makes it important that the backup copy is not only secured but also be created with an air gap.
By some estimates close to two-thirds of an enterprise’s data could be in end-user control. Along with a strategy to protect servers, it is critical to have a strategy that protects SaaS data in the cloud as well as on user endpoints.
What to back up?
Backup strategies often focus only on central data stores like file servers and database servers. IT teams often tend to ignore data in end-user control – such as on endpoints or in SaaS services. By some estimates close to two-thirds of an enterprise’s data could be in end-user control. Along with a strategy to protect servers, it is critical to have a strategy that protects SaaS data in the cloud as well as on user endpoints.
My backups are encrypted – isn’t that enough?
It is important to secure backups using encryption, but banks also need to ask themselves how defensible their position is with respect to privacy. Encryption can provide security from external actors, but to achieve data privacy, encryption needs to be coupled with a strict separation of duties or a segregation of duties. True privacy is achieved when the backup data stored in the storage target (cloud or otherwise) is inaccessible to anybody by the bank.
The data should be off-limits to everybody else, including the backup vendor or the cloud/SaaS vendor. We call this Zero-Knowledge-Privacy. If the bank is using a SaaS service for backup, then it is important to make sure that they can change their encryption keys at any time.
At Parablu, we develop products to secure data for enterprises, including data protection in the financial service industry. Many of the above data points are things we’ve learned in the process of speaking to our customers and solving problems for them. If you have a perspective on data protection, security, or privacy, we’d love to hear from you. Please write to us at info@parablu.com.
Data Protection with Zero Cost Storage for Backup.






